Thank you for applying for our Spring 2026 Synchrony Fellowship.
Congratulations to the recipients of the Synchrony Graduate Fellowship for Spring 2026:
- Colin Finkbeiner
- Richard Lourie
- Zhelun Rong

Meet Our Awarded Spring 2026 Synchrony Fellowship Candidates
What practical impact will your research eventually have?
My research focuses on understanding and strengthening security and privacy properties of decentralized-based blockchain systems, their supporting infrastructure (e.g., blockchain oracles), as well as decentralized applications (dApps) built on top of them. A key part of my work is studying how security, privacy, and financial incentives interact within these protocols. As decentralized infrastructure increasingly supports high-value use cases—such as billions of dollars in decentralized financial (DeFi) services—it becomes critical to analyze how systems components interoperate, what vulnerabilities exists, and how to mitigate them. Advancing both the security and privacy guarantees of these systems is fundamental to the long-term viability of these decentralized alternatives to legacy systems.
What do you think is the most pressing need for improving cybersecurity?
In decentralized blockchain systems and its applications, a major cybersecurity need is a deeper understanding of how the different components of these systems interact. Blockchains, dApps, end-users, and off-chain infrastructure form an interconnected ecosystem where vulnerabilities often emerge not within a single layer but within the often-complex interactions between components. Building a holistic view of blockchain security, through improved models, tooling, and testing frameworks, alongside a clearer picture of the cross-layer risks introduced in these complex systems is essential to securing real-world deployments and the billions of dollars that underly them from sophisticated attacks.
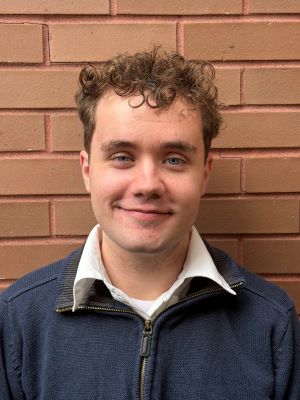
Colin Finkbeiner
What practical impact will your research eventually have?
Our research may eventually be used to simplify blockchain protocols that are in widespread use. In particular, we hope to leverage efficiently decodable error-correcting codes to reduce the amount of peer-to-peer communication required for participants to learn the blockchains held by other participants in the network. Our method is sufficiently general to allow application to many different protocols.
What do you think is the most pressing need for improving cybersecurity?
The most pressing need is building systems that remain secure even when the human user isn’t perfect. The overwhelming majority of real-world compromises come from social engineering and usability failures. Improving security will depend on designing infrastructure that is resilient to large-scale human error.

Richard Lourie
What practical impact will your research eventually have?
My current research examines how prior scam experiences, along with cognitive, psychological, and behavioral factors, shape people's ability to recognize various emerging scams (e.g., romantic and AI-generated scams). This investigation has the potential to create meaningful change in several areas.
At the individual level, our findings can help inform the development of personalized risk assessment tools. These tools would evaluate a person’s vulnerability by analyzing their exposure history, emotional responses, psychological traits, and behavioral patterns. Rather than providing generic warnings, the tools would identify specific vulnerabilities and tailor interventions to address those weaknesses.
What do you think is the most pressing need for improving cybersecurity?
The most pressing need is to address the human cognitive and psychological dimensions of cybersecurity. We need behaviorally informed approaches rather than relying predominantly on technical solutions. Cybersecurity systems sometimes should be person-centered and context-specific, rather than designed as one-size-fits-all. Ultimately, cybersecurity is a fundamentally human problem that requires interdisciplinary collaboration to develop solutions aligned with human nature.

Zhelun Rong
Meet Our Awarded Fall 2025 Synchrony Fellowship Candidates
What practical impact will your research eventually have?
My research aims to make cyber-physical systems (CPS)—such as autonomous vehicles, power grids, and intelligent transportation systems—more secure, resilient, and privacy-preserving in the face of cyberattacks and communication failures. By developing distributed control frameworks that remain stable under stealthy false data injection and denial-of-service attacks, my work enables these systems to operate safely and reliably even in adversarial environments. Additionally, the privacy-preserving mechanisms I design allow agents to coordinate securely without exposing sensitive internal states, which is crucial for real-world deployment in partially trusted or competitive settings. Ultimately, this research will support the creation of scalable, real-time CPS that can be trusted with safety-critical operations in our increasingly interconnected world.
What do you think is the most pressing need for improving cybersecurity?
The most pressing need in cybersecurity today is bridging the gap between theoretical resilience and real-world deployability. While many secure algorithms exist on paper, they often assume unrealistic attacker models, ignore system dynamics, or require computationally intensive detection. In safety-critical CPS, we need control strategies that are not only robust to evolving threats but also lightweight, real-time, and capable of maintaining performance under partial system compromise. In addition, there’s a growing need for privacy without encryption—methods that can guarantee confidentiality and control fidelity without incurring the latency of cryptographic protocols. Combining system-theoretic resilience, privacy guarantees, and real-time adaptability is the frontier of practical, scalable cybersecurity.
What practical impact will your research eventually have?
JavaScript is widely used in web programming and notably offloads computation to the client side, making it a common attack vector. Malicious developers frequently employ various code obfuscation techniques—such as string manipulation, encoding, and logic structure obfuscation—to evade malware detection or at least hinder analysis. Consequently, detecting malicious JavaScript code snippets before execution have been a key research focus. Deobfuscation is a prominent method for recovering original program logic and determining the intent of obfuscated code. However, existing deobfuscators rely heavily on traditional methods of source code analysis, such as static and dynamic analysis, which face limitations in scalability and capturing the semantic complexities of JavaScript. Emergent reasoning capabilities-particularly the logical reasoning of large language models (LLMs)-demonstrate significant potential in understanding code semantics. Our work proposes a hybrid approach, combining classical source code analysis tools with LLMs to deobfuscate JavaScript. We aim to replace heuristic-based rules in existing deobfuscators - which typically require substantial manual intervention - with LLMs that leverage advanced reasoning capabilities to autonomously infer code semantics. Our solution will enable faster, more accurate detection of malicious JavaScript — reducing manual effort in reverse-engineering obfuscated attacks, proactively identifying vulnerable dependencies in software supply chains (e.g., npm), and providing a scalable framework to adapt to evolving obfuscation tactics, ultimately hardening web applications against zero-day exploits.
What do you think is the most pressing need for improving cybersecurity?
In term of securing JavaScript code, the most critical need is scalable, AI-augmented defenses that autonomously decode advanced obfuscation by understanding code semantics. This requires moving beyond heuristic-based tools toward systems that harness large language models (LLMs) for real-time threat detection, particularly to protect open-source ecosystems where conventional methods fail against sophisticated supply chain attacks.

Yi Zhang

Ziqin Liu
What practical impact will your research eventually have?
My research focuses on computer vision security, where I apply deep learning techniques to image data and investigate how to make these systems more robust and trustworthy. As AI systems are increasingly deployed in high-stakes domains like autonomous driving, facial recognition, and election technologies, ensuring their security is critical. Specifically, I'm currently working on a project with the UConn Voter Center, identifying vulnerabilities in machine learning systems used in voting systems. The ultimate goal of this work is to understand how these systems can fail — and to develop strategies that make them more secure, transparent, and resilient to attacks. In the long term, this research will help inform the design of safe, trustworthy AI in democratic infrastructure.
What do you think is the most pressing need for improving cybersecurity?
In today’s fast-moving AI landscape, one of the most pressing needs is ensuring that machine learning systems — especially those used in sensitive and critical applications — are not just performant, but also secure, interpretable, and robust to adversarial manipulation. As my work in election security highlights, it's not enough for AI to be accurate under ideal conditions — we need it to behave reliably under stress, be resistant to attacks, and remain transparent to stakeholders. Building this kind of resilience into AI systems is key to earning public trust and preventing serious real-world failures and is a core focus of my research.

Aayushi Verma

Spring 2026 Awards

Fall 2025 Awards
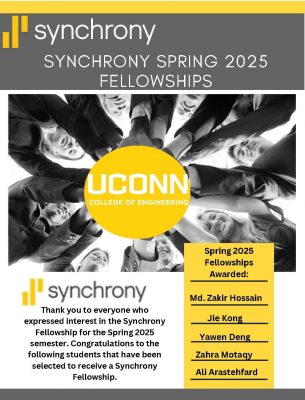
Spring 2025 Awards